Home »
Shadow Government Agencies/ Initiatives
» Threat Matrix
Threat Matrix
Written By Michael Reign on Tuesday, May 12, 2015 | 10:17 PM
An electronically transcribed counterintelligence and antiterrorist information and assessment network that originated in Pakistan in 2011 under the political regime of then Prime Minister Yousaf Raza Gillani; the development of the program coincided with the Pakistani government’s renewed sense of focus and commitment in the evaluation of perceived internal and external threats challenging the nation’s security. The database gauges the operational priorities of the military, pairing these findings with statistical probability and mathematically engendered algorithms emphasizing threat potential. Several nondescript variants of the aforementioned topology were later adopted by a myriad of interagency contingents within the U.S. Federal Government under the guise of cyber protectionism. These antecedent incarnations of the prior stated provision were eventually integrated into a more comprehensive system incorporating the use of metrically deduced arrays - numeric indices later assigned a degree of intrinsic value based on the observable activities¹ of certain groups or individuals deemed hazardous to the continuity of governance.
CONCLUSION: The introduction and eventual inclusion of a numerically inspired method of assignation into the structure and framework of federally-coordinated data aggregation services/ directories (MAIN CORE, ADEX List, CODIS, National Security Agency Utah Data Center, etc.) has ushered in a new era of suspicion among its progenitors, where the presumption of innocence in legal proceedings is oftentimes mitigated, hastening the emergence of a government-sanctioned prison-industrial complex.
¹ The assigned value of an individual’s overall risk or threat matrix potentiality is based on:
1) Electronically-transcribed communications ledgers (Email correspondence, social media account registry information, site specificity, etc.)
The codification of internet-specific threat analogs are often inclusive of the following:
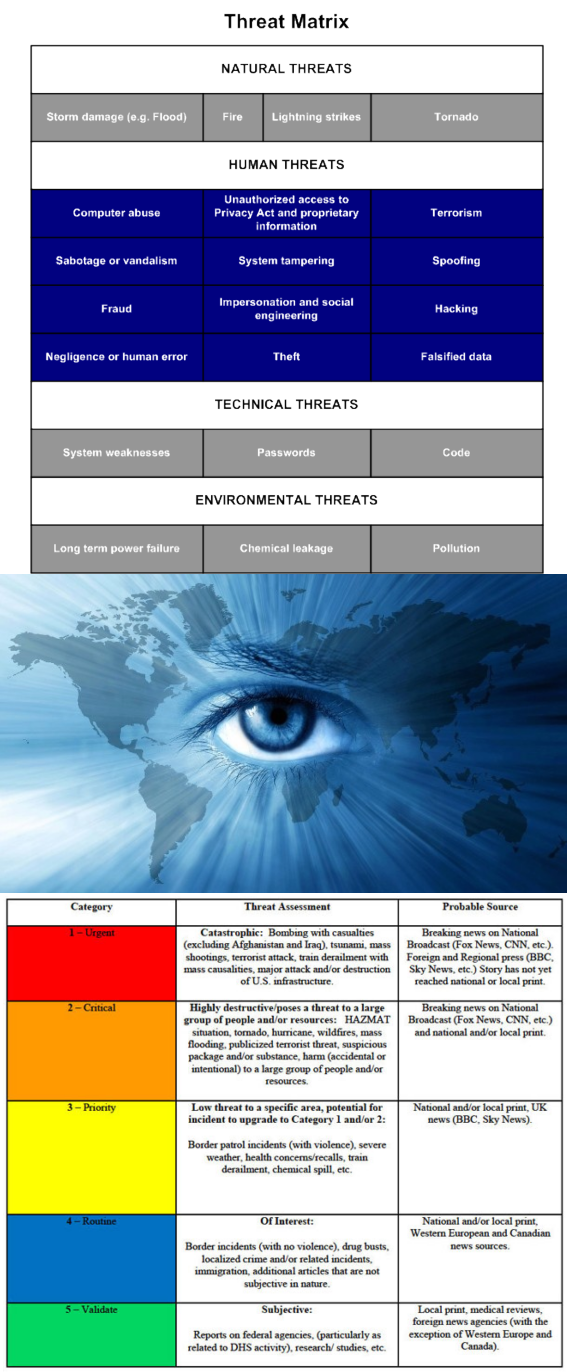
Figure 1. Cyber-Security relevant Threat Matrix assessment sample - the Federal Government has adopted a similar system of vulnerability assessment in the categorization of systemic hazards to the viability of its operational continuance. It relies on the presence of attack vectors or methods of infiltration as its principal standard of determination, with phishing offensives, unsecured wireless networks, removable media (portable hardware attachments - USB, Universal Serial Bus, drive extensions), mobile communications devices, malignant web processes/ components, viral intrusion, and the introduction of malicious software applications or malware recognized as aspects of attribution.
Figure 2. Nationally indexed threat assessment standard
Figure 3. Cyber Threat Taxonomic Standard
2) Political affiliation (TEA Party sponsors, fiscal conservationists, anti-immigration activists, proponents of religious freedom, libertarian traditionalists, social idealists, Constitutionalists - predominantly 2nd Amendment preservationists, etc.)
3) Religious persuasion (Christian fundamentalists, pro-life/ anti-abortion activists, non-secularist affiliates, etc.)


































0 comments:
Speak your mind and let your voice be heard.
This is a censorship free discussion area, however, any comments that deviate from the content presented on this site will be subject to removal without notice.